The Anatomy of a Real Estate Wire Fraud Scam
The Money Is Gone Before Anyone Realizes What Happened
The closing was scheduled for a Thursday morning. The buyers had been under contract for 42 days. The inspection went well. The mortgage commitment came in on time. Everything was moving exactly as it should.
Then, on Tuesday afternoon, the buyers received an email from what appeared to be their title company. Routing number. Account number. A note that said their previous instructions had been updated due to a banking system change. Please wire by Wednesday end of business to avoid any delay at the table.
They wired $94,000.
Their real title company had never sent that email.
This is not a cautionary tale from five years ago. Real estate fraud accounted for 12,368 complaints and $275.1 million in losses in 2025 alone — and the number keeps climbing. Real estate fraud losses jumped from $173 million in 2024 to $275.1 million in 2025, a 59% increase in a single year. HousingWireScotsman Guide
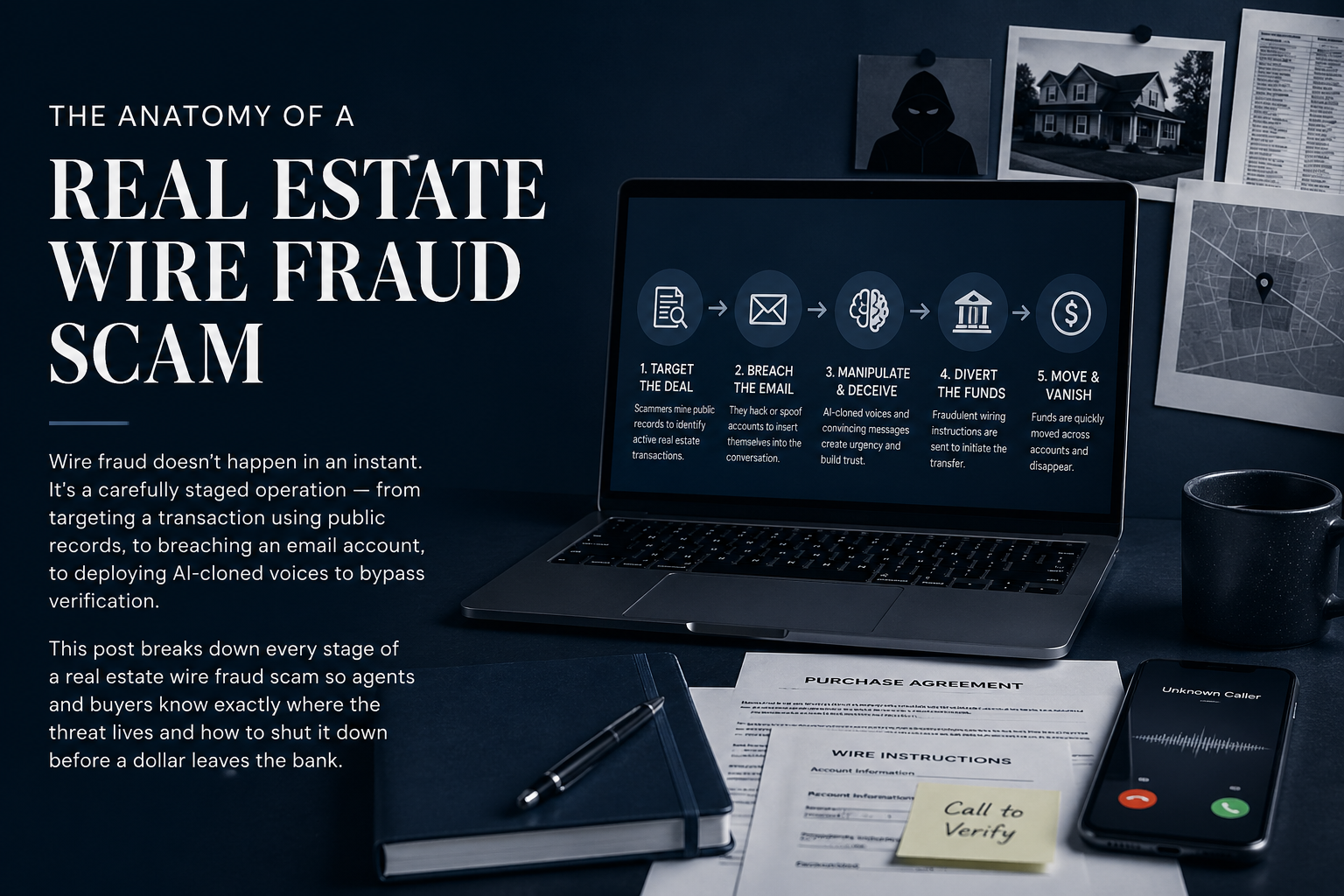
What's driving that surge isn't luck or coincidence. It's architecture. Wire fraud in real estate follows a deliberate, multi-stage operation — and understanding every layer of it is the first step toward stopping it.
This post walks through exactly how a real estate wire fraud scam is built, from the initial reconnaissance to the moment the money disappears, and what agents, coordinators, and clients can do at each stage to interrupt it.
Stage One: The Hunt — How Fraudsters Choose Their Targets
Before a single fraudulent email is ever sent, a significant amount of work has already taken place. Wire fraud in real estate is not random. It is targeted, researched, and timed.
In a typical scenario, cybercriminals identify a pending sale transaction and then build a profile of the parties — including the title company, real estate agents, and the buyer and seller. They hack into one or more parties' email account and monitor email traffic for their opportunity to strike, usually sending false wire instructions that divert deposits, closing costs, and even mortgage payoff funds from their intended destination. National Association of REALTORS
The targeting process often begins with publicly available information. MLS listings show property addresses, list prices, and listing dates. County property records reveal ownership history and estimated equity. Social media posts from agents and even buyers can reveal closing timelines. From these sources alone, a fraudster can identify which transactions are active, how large the transfer is likely to be, and approximately when the money will move.
Real estate is uniquely vulnerable because open-source intelligence is available from property records and listings, real estate businesses don't require robust IT infrastructure to operate, and cybersecurity standards are often left up to state-level jurisdictions. Certifid
Once a target transaction is identified, the fraudster needs access to the communication flow. That means getting into someone's inbox.
Stage Two: The Breach — Getting Inside the Email Chain
The entry point is almost always phishing. A fraudster sends a convincing email to a real estate agent, title company employee, or attorney — often disguised as a DocuSign request, a software update notice, or a message from a familiar vendor. The recipient clicks a link. Credentials are harvested. The inbox is now accessible.
These criminals deploy a complex phishing scam, often using bogus emails, phone numbers, and websites to impersonate a known and trusted party. The con may include attempts to trick buyers into providing additional personal information or clicking links that download malware or otherwise facilitate access to login and password data. Patten Title Company
What happens next is not what most people expect. The fraudster does not immediately strike. They wait.
The new scammer is not the stereotype from old movies. Today's fraudsters are patient, organized, and skilled at digital impersonation. They learn how your title company communicates. They mimic the tone of your emails. They follow the timeline of your transaction and strike when you are distracted and rushing to the finish line. Barnes Walker
Sometimes a compromised inbox is monitored for weeks before a move is made. The fraudster reads every email. They learn the names of the buyers, the sellers, the lender, the co-op agent. They know the property address, the purchase price, the closing date, and the approximate wire amount. By the time they act, they know more about the transaction than some of the legitimate parties involved.
According to the State of Wire Fraud 2025 Report, 17% of title companies sent client money to fraudulent accounts — a sobering measure of how effectively fraudsters are penetrating these systems. Certifid
Stage Three: The Setup — Building the Impersonation
With full transaction details in hand, the fraudster now constructs the attack. The goal is to create a communication that is indistinguishable from the real thing.
Using stolen information, criminals create spoofed email addresses and lookalike domains that appear nearly identical to the legitimate ones. A common tactic is to add a single character or swap a letter — for example, "titlecompany-llc.com" instead of "titlecompany.com." DomiDocs
The email they build will use the correct company name, the correct agent's name, the correct property address, and the correct closing date. It will be written in the same tone as previous emails in the chain. It will include a professional signature block. In many cases, it will reference specific details — the loan amount, the inspection date, the names of parties — that only someone inside the communication thread would know.
The email address may look legitimate, and could appear to come from the title company, loan officer, or someone closely involved with the real estate transaction. An extra letter in the address is easy to overlook, especially if everything else in the email looks legitimate. LendingTree
This is what makes the scam so difficult to catch. There is no obvious grammatical error, no weird formatting, no message from a stranger. The email looks exactly like every other email the buyer has received throughout the transaction — because it was built using those emails as a template.
Stage Four: The Strike — Timing the Fraudulent Wire Request
The fraudulent email is almost never sent at the beginning of a transaction. It arrives close to closing — when emotions are high, deadlines are real, and the buyer is primed to act quickly on any instruction related to their closing funds.
Scammers target homebuyers during the closing process because it is a stressful time with many moving pieces. They know your emotions are running high with excitement and overwhelm. The "new instructions" will direct you to wire money to the wrong bank account, which the fraudsters own. Scammers prefer wiring because it is difficult to cancel or undo a wire transfer. LendingTree
The language in the email is engineered to suppress verification instincts. Subject lines read: "URGENT: Updated Wire Instructions Before Thursday Closing" or "Action Required — Please Resend Wire to Corrected Account." The body of the email includes a plausible explanation — a banking system migration, a new escrow account, a correction to a previously sent instruction — and a deadline that creates pressure to act now rather than call and confirm.
That kind of message can feel believable because buyers are already expecting payment instructions. They may also be nervous about delaying the closing, losing the house, or creating problems at the last minute. That pressure is exactly what the scammer wants. CYBERRISKED
Emails that demand urgent action, particularly those sent at the end of the month or the beginning of bank holidays, are especially common — and not by accident. Fraudsters know that banks are harder to reach at those moments, and that recovery windows shrink dramatically over weekends and holidays. J.P. Morgan
Stage Five: The Evolution — AI, Voice Cloning, and Deepfakes
What was already a sophisticated scam has entered a new era. Fraudsters are no longer limited to email impersonation. They now have tools that allow them to clone voices, fabricate phone calls, and in some cases, generate synthetic video of people who don't exist.
Fraudsters are successfully mimicking voices of real people involved in a transaction, often using short audio samples pulled from voicemail or LinkedIn. In several cases, the voice itself sounded convincing enough that the call passed what used to be considered a verification step. HousingWire
Think about what this means for a standard protection protocol. For years, agents and title companies have told clients: if you receive an email with new wire instructions, call to verify. But if the fraudster can clone the voice of the title closer and call the buyer back to confirm the fraudulent instructions, that verification step has been neutralized.
AI-driven voice cloning fuels sophisticated "vishing" attacks, bypassing email defenses by creating urgent, realistic calls that exploit instinctive responses, elevating wire fraud and unauthorized data access risks for agents and brokerages. Inman
Impersonation scams showed a jaw-dropping 1,400% year-over-year growth in 2025, and scams involving AI components extract 4.5 times more money than traditional scams, averaging $3.2 million per operation. Titlerate
The AI tools behind this are not expensive or hard to access. A deepfake video demonstration at a recent conference cost $10 online and was developed in an afternoon using a single image of the target, a single image of the substitute face, and basic software. "Imagine how good this will be in three years, much less 12 months," said the demonstrator. HousingWire
The implication for real estate professionals is significant: verification through a phone call is no longer sufficient on its own. Identity confirmation must happen through channels that cannot be spoofed — a callback to a number that was established and saved at the start of the transaction, not a number provided in the suspicious email or call itself.
Stage Six: The Disappearance — Why Recovery Is So Rare
The wire is sent. Within minutes, the funds begin moving through a series of accounts — often across multiple financial institutions and sometimes across international borders — specifically designed to make tracking and recovery impossible.
Once that wire hits the wrong account, it is usually gone within minutes. Banks can sometimes freeze funds if you catch it fast enough, but the window is incredibly small. Most victims never recover their money. Titlerate
The FBI's Internet Crime Complaint Center does operate a Financial Fraud Kill Chain — a rapid-response mechanism that can sometimes freeze funds before they are moved out of reach. The recovery team initiated 3,900 incidents in 2025, freezing $679 million of $1.16 billion in attempted thefts — a 58% success rate. But that success rate depends entirely on how quickly the fraud is reported. Every hour of delay reduces the odds of recovery. HousingWire
Victims of real estate wire fraud suffered a median financial loss exceeding $70,000 — making it one of the most financially devastating forms of fraud. For most buyers, that is their entire down payment. Years of savings. And it is gone not because they were careless, but because they trusted what appeared to be a legitimate email from a party they had been working with for weeks. Eftsure
Where Each Party Is Most Vulnerable
Understanding which stage of the transaction carries the highest risk for each party helps agents, coordinators, and clients know when to be most alert.
Buyers face the greatest exposure at earnest money deposit and at the closing wire — the two moments when large sums move from their bank account. First-time homebuyers are three times more likely to fall victim to wire fraud than experienced buyers, largely because they are unfamiliar with the closing process and may not know what legitimate wiring instructions look like or how they are typically communicated. DomiDocs
Sellers are targeted differently. A scammer may send a fake message to the title company, closing attorney, or settlement company pretending to be the seller. The message may say: "Please send my proceeds to this updated account." If the closing party accepts the fake instructions, the seller's proceeds may be wired to the scammer instead of the seller. CYBERRISKED
Agents are the most frequent entry point. A compromised agent inbox gives fraudsters access to every active transaction, every client's contact information, and the precise timing of upcoming closings. Requests for bulk sensitive data — lists of buyers, contacts, deposits, and loan details — can be used to impersonate parties, redirect funds, or launch targeted scams against the agent's entire client base. Gaar
Title companies and attorneys face the highest volume of attacks because they sit at the center of every transaction. Title and escrow professionals consider wire fraud to be the biggest risk to their business, and nearly all wire fraud is inherently a type of cybercrime since funds are wired digitally. Qualia Insight
How to Interrupt the Scam at Every Stage
Now that you understand the full anatomy of a wire fraud scam, here is where the operation can be stopped.
Interrupt Stage One (targeting): Limit what you share publicly about active transactions. Avoid posting closing dates, addresses, or transaction milestones on social media before closing day. Recognize that your MLS listings and county records are already public — which means fraudsters already know you have deals in play.
Interrupt Stage Two (email breach): Use strong, unique passwords for your email and transaction management accounts. Enable multi-factor authentication on every account — email, DocuSign, SkySlope, Dotloop, everything. Be skeptical of any email asking you to log in or re-verify credentials, even if it appears to come from a vendor you use regularly.
Interrupt Stage Three (impersonation setup): Establish verified contact information for every party at the very start of each file. Save phone numbers from confirmed sources, not from emails received mid-transaction. Know what your title company's actual email domain looks like — and check the full address, not just the display name, on every communication involving wiring instructions.
Interrupt Stage Four (the strike): Implement a firm, non-negotiable rule: wire instructions are never acted upon based on email alone. Every single wire, every single time, is confirmed by phone to a number that was saved at the beginning of the transaction. Urgency in an email is a red flag, not a reason to move faster.
Interrupt Stage Five (AI-enhanced attacks): Establish a pre-agreed code word or verification phrase with your title company and key parties at the start of the transaction — something that would only be known by the legitimate parties. If a call comes in to verify wire instructions, hang up and call back using a number you already have. Do not use the callback number provided in any suspicious communication.
Interrupt Stage Six (recovery): If money is wired to a fraudulent account, call your bank's fraud department immediately and request a wire recall. Then report to the FBI at IC3.gov within the first hour. Every minute matters. Time is the only factor you can still control at this stage.
The Role of Process in Fraud Prevention
It is worth saying clearly: wire fraud does not succeed because buyers are naive or agents are careless. It succeeds because fraudsters are patient, well-resourced, and sophisticated — and because real estate transactions, by their nature, involve high-pressure timelines, multiple email-based communications, and large sums of money moving on a schedule that is publicly knowable.
What stops fraud is not individual vigilance alone. It is process. Consistent, documented, repeatable process — one that establishes verified contacts at the start of every file, uses secure portals instead of open email for sensitive information, and requires phone confirmation for every wire regardless of how legitimate the instruction appears.
According to CertifID's CEO, "Don't delay setting up your security processes, and once you set them up, don't waiver from them. Incidents are going to happen, so prepare for that reality. Companies need clear, written response plans and they need to practice them." HousingWire
That is the standard every agent, coordinator, and title professional should be holding themselves to — not because fraud is inevitable, but because when it is attempted, process is the only thing standing between a client's life savings and a fraudster's bank account.
Work With a Transaction Coordinator Who Treats Fraud Prevention as Part of the Job
At Signed to Keys, every transaction runs through a secure client portal with one dedicated, vetted point of contact. We establish verified communication with every party at the start of every file. We never send or accept wire instruction changes via email. And we keep your clients informed — and protected — from the moment the contract is signed to the moment they get their keys.
We serve real estate agents across Pennsylvania, New Jersey, New York, Maryland, Connecticut, and Delaware.
If you want a coordinator who treats wire fraud protection as part of the transaction — not an afterthought — let's talk.
Request Your Free Consultation → signedtokeys.com
No obligation. No long-term commitment. Just 30 minutes to talk about how we protect your transactions and give you your time back.
Frequently Asked Questions
What exactly is the anatomy of a wire fraud scam?
Wire fraud in real estate follows a six-stage playbook: target identification using public records and MLS data, email breach through phishing, impersonation using spoofed domains and stolen transaction details, a timed strike with fraudulent wire instructions, escalating AI-enhanced tactics including voice cloning, and rapid disappearance of funds through layered accounts. Understanding each stage helps agents and clients know when and where to be most alert.
How do fraudsters know the details of my transaction?
Through two primary channels. First, publicly available information — MLS listings, county property records, and social media posts — tells fraudsters which transactions are active and approximately how large the wire will be. Second, and more dangerously, they gain access to the email accounts of agents, title companies, or attorneys through phishing attacks, then monitor every communication in the chain for weeks before striking.
How long does a fraudster monitor an inbox before striking?
There is no fixed timeline, but patience is a defining characteristic of sophisticated wire fraud operations. Fraudsters have been known to monitor compromised inboxes for several weeks, reading every email, learning every party's name, and tracking the transaction toward its closing date before sending a single fraudulent message.
Why is the closing wire such a high-risk moment?
Because it combines the three conditions fraudsters rely on most: a large sum of money moving in a defined window of time, high emotional stakes that reduce critical thinking, and a deadline that creates pressure to act without verifying. Buyers who have been working toward closing for 30 to 60 days are primed to follow any instruction that appears to come from a trusted party — and fraudsters time their attack precisely to exploit that state of mind.
Can voice calls be faked too, or just emails?
Yes — and this is where the threat has evolved most dramatically. AI-powered voice cloning now allows fraudsters to replicate the voice of a title closer, an attorney, or even an agent using just a few seconds of audio pulled from voicemail or LinkedIn. In several documented 2025 cases, cloned voices passed what had previously been considered a reliable verification step. This means a phone call to a number found in a suspicious email is no longer sufficient verification — you must call back using a number saved independently at the start of the transaction.
What should I do the moment I suspect a wire fraud attempt?
Stop. Do not wire anything. Examine the full email address of the sender — not just the display name — character by character. Call the party in question using a phone number you saved before the suspicious email arrived. If you confirm the email was fraudulent, alert your agent and title company immediately so they can secure their systems and warn other clients. Report the attempt to the FBI at IC3.gov even if no money was sent — it helps the agency track patterns and protect others.
What if the money was already wired?
Act within hours, not days. Call your bank's fraud department immediately and request a wire recall. Then report to the FBI's Internet Crime Complaint Center at IC3.gov and file a police report, saving all email communications as evidence. The FBI's Financial Fraud Kill Chain has a meaningful success rate at freezing funds — but only when the report is filed quickly. Recovery odds drop sharply after the first few hours as funds move through additional accounts.
How does working with a transaction coordinator reduce wire fraud risk?
A professional transaction coordinator establishes verified contact information for every party at the start of every file, sends introduction emails so all parties know who to expect communications from, uses secure client portals that remove sensitive information from open email chains, and maintains a single, vetted phone number for every party so verification calls go to the right place. This structured process removes many of the entry points fraudsters rely on — particularly the confusion that arises when buyers aren't sure who they should be hearing from or what legitimate wiring instructions actually look like.
Is wire fraud more common in certain states or markets?
Fraudsters target high-value markets, high-volume markets, and markets with a large share of remote or out-of-state buyers — because those transactions often involve less in-person contact and more reliance on email-based communication. In the Northeast, which has all three of those characteristics across markets like New York, New Jersey, and Pennsylvania, wire fraud risk is significant and growing. State-specific transaction processes and closing requirements can also create additional complexity that fraudsters exploit.
What is the single most effective thing an agent can do right now?
Establish a firm protocol — for yourself and for every client — that wire instructions will never change via email alone, full stop. Communicate this rule explicitly at the first meeting, not the day before closing. Give every client a verified phone number for the title company or closing attorney, saved in their contacts from day one. And use a transaction coordination process that builds secure communication practices into every file by default, not as an afterthought.